- All
- AI
- Business
- Business Continuity
- Cloud
- Cybersecurity
- IT Management
- Microsoft
- New Technology
- Online Presence
- Productivity
- Working From Home
Micro-SaaS Vetting: The 5-Minute Security Check for Browser Add-ons
Browser add-ons have a funny reputation. They feel “small”. A quick install. A tiny productivity boost. A harmless little helper that lives in your toolbar. But in practice, a browser extension is more like a micro-SaaS vendor sitting inside your browser session. It can see what you see, interact with the pages you open, and […]
LinkedIn “Social Engineering”: Protecting Your Staff from Fake Recruitment Scams
A fake recruiter message is one of the cleanest social engineering tricks around because it doesn’t look like a trick. That’s why LinkedIn recruitment scams work so well inside real businesses. They don’t arrive as malware. They arrive as a normal conversation that nudges someone toward one small action: click this link, open this file, […]
“Clean Desk” 2.0: Securing Your Home Office from Physical Data Leaks
In the traditional office, a “Clean Desk” policy was a simple habit: shred the sensitive stuff, lock it away, and don’t leave passwords where someone can see them. In 2026, the same idea still matters but the “desk” has changed. For many teams, the home office is now the default workspace, and that means physical […]
The Essential Checklist for Securing Company Laptops at Home
At home, security incidents don’t look like dramatic movie hacks. They look like stepping away from your laptop during a delivery, or leaving it unlocked while you grab something from another room. Those ordinary moments, repeated over time, are how work devices end up exposed. A remote work security checklist focuses on simple, practical controls […]
The 2026 Guide to Uncovering Unsanctioned Cloud Apps
If you want to uncover unsanctioned cloud apps, don’t begin with a policy. Start with your browser history. The cloud environment most businesses actually use rarely matches the one shown on the IT diagram. It’s built through countless small shortcuts: a “just this once” file share, a free tool that solves one problem faster, a […]
Stop Ransomware in Its Tracks: A 5-Step Proactive Defense Plan
Ransomware isn’t a jump scare. It’s a slow build. In many cases, it begins days, or even weeks, before encryption, with something mundane, like a login that never should have succeeded. That’s why an effective ransomware defense plan is about more than deploying anti-malware. It’s about preventing unauthorized access from gaining traction. Here’s a five-step […]
Zero-Trust for Small Business: No Longer Just for Tech Giants
Think about your office building. You probably have a locked front door, security staff, and maybe even biometric checks. But once someone is inside, can they wander into the supply closet, the file room, or the CFO’s office? In a traditional network, digital access works the same way, a single login often grants broad access […]
The Supply Chain Trap: Why Your Vendors Are Your Biggest Security Risk
You invested in a great firewall, trained your team on phishing, and now you feel secure. But what about your accounting firm’s security? Your cloud hosting provider? The SaaS tool your marketing team loves? Each vendor is a digital door into your business. If they leave it unlocked, you are also vulnerable. This is the […]
The “Insider Threat” You Overlooked: Proper Employee Offboarding
Imagine a former employee, maybe someone who didn’t leave on the best terms. Their login still works, their company email still forwards messages, and they can still access the project management tool, cloud storage, and customer database. This isn’t a hypothetical scenario; it’s a daily reality for many small businesses that treat offboarding as an […]
The 2026 Hybrid Strategy: Why “Cloud-Only” Might Be a Mistake
Since cloud computing became mainstream, promising agility, simplicity, offloaded maintenance, and scalability, the message was clear: “Move everything to the cloud.” But once the initial migration wave settled, the challenges became apparent. Some workloads thrive in the cloud, while others become more complex, slower, or more expensive. The smart strategy for 2026 is a pragmatic […]
Managing “Cloud Waste” as You Scale
When you first move your data and computing resources to the cloud, the bills often seem manageable. But as your business grows, a worrying trend can appear. Your cloud expenses start climbing faster than your revenue. This is not just normal growth, it is a phenomenon called cloud waste, the hidden drain on your budget […]
Beyond Chatbots: Preparing Your Small Business for “Agentic AI” in 2026
AI chatbots can answer questions. But now picture an AI that goes further, updating your CRM, booking appointments, and sending emails automatically. This isn’t some far-off future. It’s where things are headed in 2026 and beyond, as AI shifts from reactive tools to proactive, autonomous agents. This next wave of AI is called “Agentic AI.” […]
The Server Refresh Deadline: Why Windows Server 2016’s End of Support Should Drive Your Cloud Migration Plan
Time moves fast in the world of technology, and operating systems that once felt cutting-edge are becoming obsolete. With Microsoft having set the deadline for Windows Server 2016 End of Support to January 12, 2027, the clock is ticking for businesses that use this operating system. Once support ends, Microsoft will no longer provide security […]
The MFA Level-Up: Why SMS Codes Are No Longer Enough (and What to Use Instead)
For years, enabling Multi-Factor Authentication (MFA) has been a cornerstone of account and device security. While MFA remains essential, the threat landscape has evolved, making some older methods less effective. The most common form of MFA, four- or six-digit codes sent via SMS, is convenient and familiar, and it’s certainly better than relying on passwords […]
The Daily Cloud Checkup: A Simple 15-Minute Routine to Prevent Misconfiguration and Data Leaks
Moving to the cloud offers incredible flexibility and speed, but it also introduces new responsibilities for your team. Cloud security is not a “set it and forget it” type task, small mistakes can quickly become serious vulnerabilities if ignored. You don’t need to dedicate hours each day to this. In most cases, a consistent, brief […]
The “Deepfake CEO” Scam: Why Voice Cloning Is the New Business Email Compromise (BEC)
The phone rings, and it’s your boss. The voice is unmistakable; with the same flow and tone you’ve come to expect. They’re asking for a favor: an urgent wire transfer to lock in a new vendor contract, or sensitive client information that’s strictly confidential. Everything about the call feels normal, and your trust kicks in […]
Securing the ‘Third Place’ Office: Policy Guidelines for Employees Working from Coffee Shops and Coworking Spaces
The modern office extends far beyond traditional cubicles or open-plan spaces. Since the concept of remote work became popularized in the COVID and post-COVID era, employees now find themselves working from their homes, libraries, bustling coffee shops, and even vacation destinations. These environments, often called “third places,” offer flexibility and convenience but can also introduce […]
AI’s Hidden Cost: How to Audit Your Microsoft 365 Copilot Usage to Avoid Massive Licensing Waste
Artificial Intelligence (AI) has taken the business world by storm, pushing organizations of all sizes to adopt new tools that boost efficiency and sharpen their competitive edge. Among these tools, Microsoft 365 Copilot rises to the top, offering powerful productivity support through its seamless integration with the familiar Office 365 environment. In the push to […]
The Smarter Way to Vet Your SaaS Integrations
Your business runs on a SaaS (software-as-a-service) application stack, and you learn about a new SaaS tool that promises to boost productivity and streamline one of your most tedious processes. The temptation is to sign up for the service, click “install,” and figure out the rest later. This approach sounds convenient, but it also exposes […]
How to Use Conditional Access to Grant and Revoke Contractor Access in 60 Minutes
Managing contractor logins can be a real headache. You need to grant access quickly so work can begin, but that often means sharing passwords or creating accounts that never get deleted. It’s the classic trade-off between security and convenience, and security usually loses. What if you could change that? Imagine granting access with precision and […]
How to Implement Zero Trust for Your Office Guest Wi-Fi Network
Guest Wi-Fi is a convenience your visitors expect and a hallmark of good customer service. But it’s also one of the riskiest points in your network. A shared password that’s been passed around for years offers virtually no protection, and a single compromised guest device can become a gateway for attacks on your entire business. […]
6 Ways to Prevent Leaking Private Data Through Public AI Tools
We all agree that public AI tools are fantastic for general tasks such as brainstorming ideas and working with non-sensitive customer data. They help us draft quick emails, write marketing copy, and even summarize complex reports in seconds. However, despite the efficiency gains, these digital assistants pose serious risks to businesses handling customer Personally Identifiable […]
5 Ways to Implement Secure IT Asset Disposition (ITAD) in Your Small Business
Even the most powerful IT hardware today will eventually become outdated or faulty and will need to be retired. However, these retired servers, laptops, and storage devices hold a secret: they contain highly sensitive data. Simply throwing them in the recycling bin or donating them without preparation is a compliance disaster and an open invitation […]
3 Simple Power Automate Workflows to Automatically Identify and Terminate Unused Cloud Resources
The cloud makes it easy to create virtual machines, databases, and storage accounts with just a few clicks. The problem is, these resources are often left running long after they’re needed. This “cloud sprawl,” the unmanaged growth of cloud resources, can quietly drain your budget every month. According to Hashi Corp’s State of Cloud Strategy […]
Your 2025 Privacy Compliance Checklist and What You Need to Know About the New Data Laws
Privacy regulations are evolving rapidly, and 2025 could be a pivotal year for businesses of all sizes. With new state, national, and international rules layering on top of existing requirements, staying compliant is no longer optional. A basic policy won’t suffice; you need a comprehensive 2025 Privacy Compliance Checklist that clearly outlines the latest changes, […]
The SMB Guide to Making Your Website and Documents Digitally Accessible
Have you ever thought about how many potential customers leave your website because of accessibility issues? It’s not just a guess. A UK Click-Away Pound survey found that 69% of disabled internet users leave websites that aren’t accessible. For small and medium businesses, this represents a significant missed opportunity. So, how do you make your […]
The Hidden Risk of Integrations: A Checklist for Vetting Third-Party Apps (API Security)
Modern businesses depend on third-party apps for everything from customer service and analytics to cloud storage and security. But this convenience comes with risk, every integration introduces a potential vulnerability. In fact, 35.5% of all recorded breaches in 2024 were linked to third-party vulnerabilities. The good news? These risks can be managed. This article highlights […]
The AI Policy Playbook: 5 Critical Rules to Govern ChatGPT and Generative AI
ChatGPT and other generative AI tools, such as DALL-E, offer significant benefits for businesses. However, without proper governance, these tools can quickly become a liability rather than an asset. Unfortunately, many companies adopt AI without clear policies or oversight. Only 5% of U.S. executives surveyed by KPMG have a mature, responsible AI governance program. Another […]
How to Use a Password Manager and Virtual Cards for Zero-Risk Holiday Shopping
Have you ever been concerned about your credit card or personal data getting stolen while shopping online? You’re not alone. Each holiday season, as millions of shoppers flock online for convenience, hackers ramp up their activity. The Federal Trade Commission (FTC) has warned that scammers often create fake shopping websites or phishing emails to steal […]
Beyond Licensing: How to Stop Wasting Money onYour Microsoft 365 Security and Copilot Add-Ons
Microsoft 365 is a powerful platform that helps a business in many ways. It boosts collaboration and streamlines operations, among other benefits. However, many companies waste money on unnecessary licenses and features that are not fully used. Fortunately, you can avoid this waste and take your business to the next level by adopting smarter use […]
Your Business’s Digital Compass: Creating an IT Roadmap for Small Business Growth
Small businesses often struggle to leverage technology effectively. It can be a challenge just to survive, much less thrive. In many cases, they instinctively fall back on a reactive approach to IT challenges, rather than planning and acting proactively. That’s where an IT roadmap can help. It becomes a digital compass for organizations, a strategic […]
Navigating Cloud Compliance: Essential Regulations in the Digital Age
The mass migration to cloud-based environments continues as organizations realize the inherent benefits. Cloud solutions are the technology darlings of today’s digital landscape. They offer a perfect marriage of innovative technology and organizational needs. However, it also raises significant compliance concerns for organizations. Compliance involves a complex combination of legal and technical requirements. Organizations that […]
Leveraging Microsoft Forms for Data Collection & Surveys
Data has become the lifeblood of every organization, regardless of industry or sector. Today, a business’s ability to collect, analyze, and act on data is not just an advantage, it’s essential for survival. Data-driven decision-making enables organizations to respond quickly to market changes, identify new opportunities, and improve operational efficiency. When decisions are backed by […]
How to Use AI for Business Productivity While Staying Cyber-Secure
Most organizations have realized that AI is not a sentient system looking to take over the world, but rather an invaluable tool. They have come to utilize it to improve their productivity and efficiency. AI solutions have been installed at an astounding rate. Some are used to automate repetitive tasks and to provide enriched data […]
Wi-Fi Performance Secrets to Boost Your Business Productivity
Nothing disrupts your workday quite like unreliable Wi-Fi. One moment everything’s running smoothly, and the next, video calls freeze, files won’t upload, and the team struggles to meet deadlines because everything’s slowed down. Being stuck in this situation is exhausting, killing productivity, and impacting the entire business. When slowdowns start happening regularly, frustration quickly builds. […]
Project Chaos to Clarity: How Microsoft Planner Transforms Small Businesses
In the past, teams relied on sticky notes and endless email threads to manage tasks. But with today’s hybrid work environments and fast-moving deadlines, that approach just doesn’t cut it anymore. Effective project management is now essential to stay on track and ahead. According to McKinsey, the average worker spends 28% of their week managing […]
Is Your Smart Office a Security Risk? What Small Businesses Need to Know About IoT
Your office thermostat, conference room speaker, and smart badge reader are convenient, but they’re also doors into your network. With more devices than ever in play, keeping track can be tough, and it only takes one weak link to put your entire system at risk. That’s why smart IT solutions matter now more than ever. […]
Invest Smart, Grow Fast: Your Small Business Guide to IT Expense Planning
Without realizing it, technology can drain your business budget. One day, everything seems manageable, and the next, you’re left wondering where all these unexpected costs are coming from. Expenses pile up quickly and become tough to track. Whoever said running a business would be easy? Here’s the good news: you don’t need to spend thousands […]
Data Quality is Your Small Business’s Secret Weapon
Nobody builds a house on a weak foundation, so why operate your business based on unreliable data? According to research, bad data costs US firms over $3 trillion every year, and roughly 40% of company goals fail as a result of inaccurate information. Data is everywhere, and if you are not utilizing it to your […]
10 Knowledge Management Strategies That Will Unlock Your Team’s Brainpower
Is your team constantly reinventing the wheel? It might be time to build a smarter way to share what you already know. Every small business runs on shared knowledge. How things work, what’s been tried, and what actually delivers. But when that knowledge isn’t documented, mistakes repeat, and progress slows. Inefficient knowledge sharing impacts businesses […]
Securing Your Supply Chain: Practical Cybersecurity Steps for Small Businesses
Picture this: your business’s front door is locked tight, alarm systems are humming, and firewalls are up, but someone sneaks in through the back door, via a trusted vendor. Sound like a nightmare? It’s happening more often than you think. Cybercriminals aren’t always hacking directly into your systems anymore. Instead, they exploit the vulnerabilities in […]
Save Time and Money by Automating Workflows with Power Automate
Let’s be honest, operating a small or medium-sized business requires wearing multiple hats. From chasing approvals to manually updating spreadsheets, it’s easy for your team to get stuck doing time-consuming tasks that drag down productivity. That’s where smart IT solutions come in, and one of the most effective tools available today is Microsoft Power Automate. […]
From Offer Letter to First Login: How IT Makes New Hire Setup Easy
There’s nothing worse than walking into a new job and spending your first day filling out forms, asking where the bathroom is, and staring at a screen that still doesn’t have your login credentials. It’s awkward, overwhelming, and not the welcome anyone hopes for. According to Gallup, only 12% of employees strongly feel that their […]
Don’t Let Outdated Tech Slow You Down: Build a Smart IT Refresh Plan
Nothing throws off your day like a frozen screen or a sluggish computer. If you run a small business, you’ve probably dealt with outdated tech more than once. Sure, squeezing extra life out of old equipment feels economical, but it often costs more in the long run. Small businesses lose approximately 98 hours per year, […]
Building a Smart Data Retention Policy: What Your Small Business Needs to Keep (and Delete)
Does it ever seem like your small business is overwhelmed with data? This is a very common phenomenon. The digital world has transformed how small businesses operate. We now have an overwhelming volume of information to manage employee records, contracts, logs, financial statements, not to mention customer emails and backups. A study by PR Newswire […]
Avoid Cloud Bill Shock: Cost Optimization Tips Every Small Business Should Know
The cloud can be your greatest asset or your biggest financial headache. One minute you’re deploying apps and scaling infrastructure, and the next you’re hit with a cloud bill that strains your budget. Sound familiar? It’s a common business problem. A study by Nextwork also shows that cloud spending is expected to increase by 21.5% […]
Simple Backup and Recovery Plans Every Small Business Needs
What would happen if your business lost all its data tomorrow? Would you be able to recover, or would it grind your operations to a halt? Every small business runs on data, which includes customer information, financial records, communications, product files, and more. Yet data security often falls to the bottom of the to-do list. […]
Remote Work Security Revisited: Advanced Strategies for Protecting Your Business in 2025
The landscape of remote work has transformed dramatically over the past several years. What began as a reactive shift to keep operations going during a major global disruption has now solidified into a permanent mode of working for many organizations, especially small businesses. If you’re running a business in this evolving digital landscape, it’s not […]
How to Choose the Right Cloud Storage for Your Small Business
Choosing the right cloud storage solution can feel a bit like standing in front of an all-you-can-eat buffet with endless options- so many choices, each promising to be the best. Making the wrong decision can lead to wasted money, compromised data, or even a productivity bottleneck. For small business owners, the stakes couldn’t be higher. […]
Can My Data Be Removed from the Dark Web?
Personal data protection is more important than ever in this digital world. The dark web is a secret part of the internet that is very dangerous because it is often used for illegal things like selling personal information. Because the dark web is decentralized and private, it is very hard to get rid of data […]
7 Unexpected Ways Hackers Can Access Your Accounts
The digital age has made our lives easier than ever, but it has also made it easier for hackers to take advantage of our online weaknesses. Hackers are getting smarter and using more creative ways to get into people’s personal and business accounts. It’s easy to think of weak passwords and phishing emails as the […]
How Do Websites Use My Data? (Best Practices for Data Sharing)
Websites store and use user data in many ways, usually to personalize content, show ads, and make the user experience better. This can include everything from basic data like the type of browser and IP address to more private data like names and credit card numbers. It’s important for people to know how this information […]
Ultimate Guide to Safe Cloud Storage
Since we live in a digital world, cloud storage is an important tool for both personal and business use. So long as they have an internet connection, users can store and get to their info from anywhere at any time. But while cloud storage is convenient, there is a chance that your data could be […]
Complete Guide to Strong Passwords and Authentication
Cyber risks are smarter than ever in today’s digital world. People and companies can lose money, have their data stolen, or have their identities stolen if they use weak passwords or old authentication methods. A strong password is the first thing that will protect you from hackers, but it’s not the only thing that will […]
What is Password Spraying?
Password spraying is a complex type of cyberattack that uses weak passwords to get into multiple user accounts without permission. Using the same password or a list of passwords that are often used on multiple accounts is what this method is all about. The goal is to get around common security measures like account lockouts. […]
10 Tips to Get the Most Out of Your Microsoft 365 Apps
Microsoft 365 is a strong set of tools created to make working together and staying safe easier on many devices and systems. It has well-known programs like Word, Excel, PowerPoint, and Outlook, as well as new ones like Teams and OneDrive. With its powerful features and cloud-based services, Microsoft 365 gives businesses a complete way […]
6 Best Cloud Storage Providers to Save Device Space
In this digital world, it’s hard to keep track of all the storage space on your devices. It’s easy for our devices to run out of room because we keep adding more photos, videos, documents, and files. Cloud storage is a convenient option because it lets people store their data online, which frees up space […]
10 Awesome Ways to Customize Your Desktop Layout
You can make your computer experience more unique by changing the style of your desktop. It lets you organize your area well, which makes it easier to get to files and programs you use often. There are many ways to change things whether you’re using Windows, macOS, or Linux. This can make a big difference […]
7 New and Tricky Types of Malware to Watch Out For
Malware is a huge threat in the digital world. It can cause a lot of damage and cost people a lot of money. As technology advances, so do the tactics used by cybercriminals. In this article, we will explore some of the newest and trickiest types of malware. 7 Malware Threats to Watch Out For […]
Where Do Deleted Files Go?
It may seem like the file is gone for good when you delete it from your computer. However, the truth is more complicated than that. A deleted file doesn’t really disappear from your hard drive; it stays there until new data fills up the space it occupied. This process might be hard to understand for […]
New Gmail Threats Targeting Users in 2025 (and How to Stay Safe)
Cybercriminals target Gmail a lot because it’s very popular. It also integrates with many other Google services. As AI-powered hacking attacks become more common, it gets harder for people to distinguish between real and fake emails. As 2025 approaches, it’s crucial for Gmail users to be aware of these new threats and take steps to […]
8 Considerations Before Buying Used Technology
We use our devices every day, so they need to work well for our needs. A device that’s slow or broken is inconvenient and can affect productivity for day-to-day tasks. But buying a brand new phone or laptop isn’t always the best option. We’ll cover eight things you should consider before making the purchase of […]
All About the New U.S. Cyber Trust Mark
The Cyber Trust Mark is a new smart device label created by the US government to prove that a device is safe. Internet of Things (IOT) devices have risen in popularity recently. Devices like smart thermostats and baby monitors make our lives easier, but also open us up to cyber threats. There were over 112 […]
Top 10 Security Tips for Mobile App Users
Mobile applications have become an integral part of our lives. We use them to browse the internet, network, communicate, and much more. But they open us up to risks caused by fraudsters who may steal information or damage our phones. According to 2024 data from Asee, over 75% of published apps have at least one […]
Is It Time for a Device Upgrade? Check for These 7 Signs
Technology is fast, and in no time, our gadgets get outdated. According to data from Statista, consumers replace their devices about every 2-3 years. Still, it can be tricky to determine when an upgrade is needed. Upgrading your device isn’t just about having the latest gadget. An up-to-date device is safer and more efficient. This […]
How Much Device Storage You Need: A Comprehensive Guide
Device storage decides how many applications, photos, and files you can retain on your device. When you run out of storage, it can affect your productivity and device performance. But finding the right storage amount isn’t always easy. We can underestimate what we need or get too much storage. This guide will help you figure […]
Spotting the Difference Between Malware and Ransomware
Malware and ransomware are two types of bad software. They can damage your computer or steal your data. Downloading this harmful software comes with serious consequences. In 2024, there were more than 60 million new strains of malware found on the internet. This is why it’s critical to understand the difference between them. This article […]
7 Ways Using AI for Work Can Get Complicated
AI is going to change how we work. It can make some tasks easier. But it can also cause problems. Let’s look at some ways AI can make work tricky. What is AI and how does it affect work? AI stands for Artificial Intelligence. The computer systems are actually able to do the things that […]
8 Ways to Organize Your Devices for Productivity
Our devices are a big part of our daily lives: work, fun, and staying in touch. Still, sometimes they make us less productive. In this article, you will learn how to organize your device. You’ll learn ways to boost your productivity and get more done. Why is device organization important? Messy devices slow us down […]
How to Minimize Ransomware Damage
Ransomware has now become a big problem for many people and businesses. It can lock up your files and make you pay money to get them back. This article will show how one can protect themselves from ransomware and what to do in case of an attack. What is ransomware? Ransomware is a type of […]
10 Steps to Prevent a Data Breach
Data breaches can harm your business. They can cost you money and trust. Let’s look at how to stop them from happening. What is a data breach? A data breach is when someone steals information. This can be names, emails, or credit card numbers. It’s bad for your customers and your business. Why should you […]
How to Spot Hidden Malware on Your Devices
Malware is bad software that can hurt your computer or phone. It can also make your device run slow and steal your info. Here is how you can spot hidden malware on your devices. What is Malware? The word “malware” is short for “malicious software.” It is a program that tries to harm your device […]
Guide to Secure File Storage and Transfers
File storage and transferring hold a very dear place in most people’s lives. However, the safety of files is really tough to maintain. In this guide, we are going to help you protect your files. We will explore ways to store and send files securely. What is secure file storage? Secure file storage protects your […]
Best Practices for Secure Data Backup
These days, everything is digital. We deal with data every day: from personal photos to work files that hold a lot of value. What happens if you lose that? Well, this is the reason behind doing secure backups of data. Let’s go through some best practices to keep your data safe and secure. What is […]
5 Common Cyber Threats in 2025 (and How To Avoid Them)
In 2025, cyber threats are in almost every nook and corner. They might be with the intent to destroy computers, steal data, or take money. Understanding what they are and how protection against them works will come in handy. What Are the Most Common Cyber Threats? They come in so many forms, some old, some […]
Can Password Managers Be Hacked?
Password managers keep our online accounts safe. They store all our passwords in one place. But are they hackable? What Are Password Managers? Password managers are like digital vaults: they save all your passwords inside themselves. You need only remember one master password, of course. This makes keeping a lot of accounts much easier to […]
10 AI Tools You Need in Your Office For Productivity
In today’s fast-moving world, everyone wants to work wiser, not harder. The involvement of AI tools will definitely help you do just that. They can make your work easier and faster. Let’s explore some AI tools that can boost productivity in your office. What Are AI Tools? AI tools are software programs that use artificial […]
What is Blockchain Technology and How Does it Work?
Blockchain technology is changing the world. It is a system designed to keep records safe and secure. But how does it work? Let’s find out more about this amazing technology. What is Blockchain? Blockchain is some kind of digital ledger. In it, information is stored in a manner that makes it hard to change. This […]
Ultimate Guide to Encryption Methods
Encryption is a method of securing information. It converts readable data into secret code. Only the right key can decode it. This guide will help you understand different encryption methods. What is Encryption? Encryption is like a secret language. It converts regular text into unreadable text. This unreadable text is called ciphertext. Only people who […]
How is Your Cyber Hygiene? Essential Tips For 2025
Cyber hygiene is super important. It’s like brushing your teeth but for your online life. Good cyber habits help keep you safe from hackers on the internet. Let’s check some easy ways to stay safe online in 2025. What is Cyber Hygiene? Cyber hygiene means the care you give to your online stuff. This includes […]
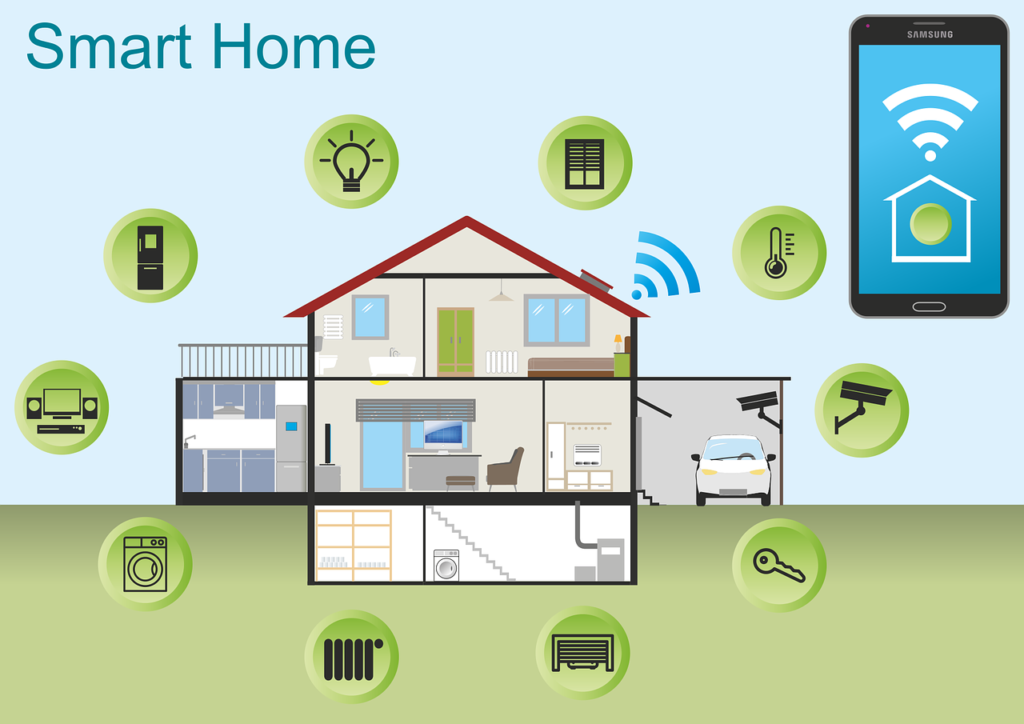
10 Tips For a Seamless Smart Home Experience
Smart homes make life easier. But setting one up can be tricky. Here’s how to make a smooth smart home system. What is a Smart Home? A smart home uses technology to control many parts of life. This includes turning lights on and off and unlocking doors. You can control these devices with your voice […]
What is Threat Exposure Management (TEM)?
Threat Exposure Management (TEM) is an important cybersecurity tool. It helps organizations find and fix weak spots in their digital systems. TEM outsmarts hackers before they break into your network. Importance of TEM Cyber attacks keep getting worse. Hackers always find new ways to break in. TEM helps businesses spot problems before they become big […]
How Password Managers Protect Your Accounts
Passwords unlock our digital lives. We use them for email, bank accounts, and more. Remembering all these passwords is hard. Password managers help us keep our accounts safe and make our lives easier. What is a Password Manager? A password manager keeps all your passwords in one place. Think of it as a digital safe […]
Innovative Solutions to IoT Device Security
The Internet of Things is growing day by day. More devices are connecting to the internet. And with that growth comes new security risks. Let’s look at some new ways to keep your IoT devices safe. What are the security risks for IoT devices? IoT devices are vulnerable to many types of threats. Some of […]
5 New Trends from a Study on the State of AI at Work
The pace of technological advancement is accelerating. This is not news to anyone wading through the ChatGPT craze. Artificial intelligence (AI) is at the forefront of this revolution. We are swiftly seeing companies adopting AI solutions. Even more rapidly are software providers like Microsoft adding AI to tools. The goal is to use AI to […]
Guide to Smart Windows 11 Settings to Boost Your Productivity
The newest Windows OS is fast gaining ground on Windows 10. As of August 2024, Windows 11 had over 31% of the Windows market share. That is bound to increase fast as Windows 10 retires in 2025. Already upgraded to the new operating system or planning to soon? Then, you’ll love these tips on optimizing […]
7 Great Examples of How AI is Helping Small Businesses
Artificial Intelligence is no longer a technology reserved for companies with big budgets. Today, small businesses can access AI tools that help in several ways. Such as streamlining operations, improving customer experiences, and boosting profits. The rise of affordable AI solutions has opened the door for small businesses. They can leverage these powerful technologies without […]
Top Technologies Transforming Customer Service Today
Customer service is at the heart of any successful business. Customer expectations continue to evolve. Companies must evolve strategies and tools used to meet those expectations. 55% of customers like self-serve customer service over speaking to a representative. Technology has become a game-changer in this regard. It offers innovative solutions that improve efficiency, personalization, and […]
Data Breach Damage Control: Avoid These Pitfalls
Data breaches are an unfortunate reality for businesses of all sizes. When a breach occurs, the immediate response is critical. How a company manages the aftermath can significantly impact its reputation. As well as financial stability and legal standing. The average cost of a data breach has reached 4.88 million USD. Effective damage control requires […]
Copilot in Teams – New Features, Agents & More
Microsoft Teams continues to evolve. It is a powerful hub for collaboration and communication in the modern workplace. With the integration of AI-driven Copilot, Teams is pushing the boundaries. It’s innovating how we interact with technology to streamline workflows. As well as improve productivity and unlock new business value. Recent updates to Copilot in Teams […]
Navigating the Challenges of Data Lifecycle Management
Data is one of the most valuable assets a business can have. Managing this data throughout its lifecycle can be challenging. Data lifecycle management (DLM) refers to several processes and policies. They govern the handling, storage, and eventual disposal of data. Businesses generate and store vast amounts of data. As this happens, the importance of […]
6 Simple Steps to Enhance Your Email Security
Email is a fundamental communication tool for businesses and individuals alike. But it’s also a prime target for cybercriminals. Cyberattacks are increasing in sophistication. This means enhancing your email security has never been more critical. Ninety-five percent of IT leaders say cyberattacks have become most sophisticated. Over half (51%) have already seen AI-powered attacks in […]
8 Strategies for Tackling “Technical Debt” at Your Company
Did your company’s software system once seem sleek and nimble? But now it resembles a tangled web of shortcuts, patches, and workarounds. Welcome to the realm of technical debt. It’s a silent saboteur that accumulates over time, threatening your efficiency. What Is Technical Debt? Think of technical debt as the interest you pay on a […]
What Things Should You Consider Before Buying a Used Laptop?
Buying a used laptop can be a great way to save money. But it comes with risks. You need to be careful and thorough in your evaluation. Otherwise, you could end up wasting your money. You can’t only look at the outside when evaluating technology. This guide will help you understand what to look for […]
Top 6 Smart Office Trends to Adopt for an Improved Workflow
The office landscape is undergoing a dramatic transformation. Gone are the days of sterile cubicles and monotonous routines. Today’s smart offices are hubs of innovation. They’re designed to empower employees, optimize workflows, and foster collaboration. This shift is driven by technology. Including smart features that seamlessly integrate into the physical workspace. But with so many […]
Windows 10: The Final Countdown – It’s Time to Upgrade Your PC
Windows 10 has served us well. But its time is running out. Microsoft plans to end support for Windows 10 on October 14, 2025. This means no more security updates, no more patches, and no more support. It’s time to upgrade to Windows 11. This is especially true for business users with many systems to […]
8 Tips for Safeguarding Your Gadgets While Traveling
Traveling with technology has become a necessity. Whether for work, communication, or entertainment, we rely heavily on our devices. But traveling exposes these gadgets to various risks. Theft, damage, and loss are common concerns. We’ve put together some helpful tips to mitigate the risk of any tech mishaps on your next trip. Follow these eight […]
Unmasking the True Price of IT Downtime
Imagine this: you walk into your office on a busy Monday morning, ready to tackle the week. But something’s wrong. Computers are unresponsive. Phones are silent. The internet is a ghost town. Your business has come to a grinding halt – victim of an IT outage. It’s a scenario every business owner fears. But beyond […]
Streamlining Success: A Guide to Task Automation for Small Enterprises
Running a small business is a whirlwind. You juggle a million tasks and wear countless hats. You also constantly fight the clock. What if you could reclaim some of that precious time? Enter task automation. It’s your secret weapon for streamlining your workflow and boosting productivity. By automating routine and repetitive tasks, small businesses can […]
Phishing 2.0: How AI is Amplifying the Danger and What You Can Do
Phishing has always been a threat. Now, with AI, it’s more dangerous than ever. Phishing 2.0 is here. It’s smarter, more convincing, and harder to detect. Understanding this new threat is crucial. A recent study found a 60% increase in AI-driven phishing attacks. This is a wake-up call that phishing is only getting worse. Here’s […]
Unified Smart Homes: How Matter is Setting a New Standard
Is your smart home turning into a smart mess? Do your smart office devices speak different languages? You’re not alone. The current smart home and office technology landscape is riddled with incompatibility issues. This forces you to juggle several apps and deal with frustrating setup processes. Smart home adoption is skyrocketing. Experts expect household penetration […]
Digital Defense: Essential Security Practices for Remote Workers
The rise of remote work has redefined the modern workplace. Gone are the days of rigid office schedules and commutes. But with this flexibility comes a new set of challenges – cybersecurity threats. Remote work environments often introduce vulnerabilities to your organization’s data and systems. 73% of executives believe that remote work increases security risk. […]
Tech-Savvy Workspaces: How Technology Drives Office Productivity
Gone are the days of paper-laden desks and rows of filing cabinets. The modern office is a hub of innovation. Technology plays a starring role in this transformation. The right tech tools can significantly boost your team’s productivity. Including streamlining workflows and fostering collaboration. Is your company leveraging technology as well as it could? This […]
AI Data Breaches are Rising! Here’s How to Protect Your Company
Artificial intelligence (AI) is rapidly transforming industries. It offers businesses innovative solutions and automation capabilities. But with this progress comes a growing concern: AI data breaches. As AI becomes more integrated into our systems, the risks increase. The data it collects, analyzes, and utilizes becomes a target. A recent study on AI security breaches revealed […]
7 Important Considerations Before You Buy Smart Home Tech
Smart homes seem like something straight out of a sci-fi movie. They have lights that respond to your voice commands and thermostats that auto-adjust. Not to mention robot vacuums that clean your floors while you relax. It’s all very tempting. But before you rush out and buy the newest gadget, there are some crucial considerations. […]
Why Continuous Monitoring is a Cybersecurity Must
Imagine this: you leave your house for vacation. You live in a shady neighborhood but feel confident your locks are secure, but you also don’t check them daily. Are they really locked and safe? A tiny crack or hidden weakness could have occurred. It’s a disaster waiting to happen. That’s the risk of neglecting continuous […]
A Simple Guide to the Updated NIST 2.0 Cybersecurity Framework
Staying ahead of threats is a challenge for organizations of all sizes. Reported global security incidents grew between February and March of 2024. They increased by 69.8%. It’s important to use a structured approach to cybersecurity. This helps to protect your organization. The National Institute of Standards and Technology (NIST) created a Cybersecurity Framework (CSF). […]
Hot off the Digital Presses… Learn About Microsoft Copilot for Finance
Microsoft Copilot has been heading up the business AI charge. It’s used in Word, Excel, Edge, Windows, and more. This genAI-powered app is also showing up in various function-related activities. The latest of which is finance processes. Microsoft Copilot for Finance is a game-changer. It injects the power of next-generation AI into the heart of […]
iPhone Running Slow? Speed It up with One of These Tips
Let’s face it, iPhones are amazing devices. But even the sleekest, most powerful iPhone can succumb to the dreaded slowdown. Apps take forever to load and scrolling feels sluggish. Pretty soon, simple tasks become frustrating ordeals. If your iPhone has gone from speedy sidekick to sluggish snail, don’t despair! We are sharing some easy tips […]
Introducing the New Microsoft Planner (Everything You Need to Know)
Calendars, task lists, and project planning are important business tools. Many people use Microsoft’s apps to power these processes. Including Planner, Microsoft To Do, and Project for the web. These tools help keep processes on track and enable task accountability. But they’re separate apps. Switching between apps can be cumbersome. It adds more complexity to […]
How to Properly Deploy IoT on a Business Network
The Internet of Things (IoT) is no longer a futuristic concept. It’s rapidly transforming industries and reshaping how businesses operate. IoT is a blanket term to describe smart devices that are internet enabled. One example is smart sensors monitoring production lines. Connected thermostats optimizing energy consumption is another. Experts project the number of connected devices […]
Here Are 5 Data Security Trends to Prepare for in 2024
With cyber threats evolving at an alarming pace, staying ahead of the curve is crucial. It’s a must for safeguarding sensitive information. Data security threats are becoming more sophisticated and prevalent. The landscape must change to keep up. In 2024, we can expect exciting developments alongside persistent challenges. Over 70% of business professionals say their […]
Google & Yahoo’s New DMARC Policy Shows Why Businesses Need Email Authentication… Now
Have you been hearing more about email authentication lately? There is a reason for that. It’s the prevalence of phishing as a major security threat. Phishing continues as the main cause of data breaches and security incidents. This has been the case for many years. A major shift in the email landscape is happening. The […]
Beware of Deepfakes! Learn How to Spot the Different Types
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve received an urgent email seemingly from your boss. But something felt off. Welcome to the world of deepfakes. This is a rapidly evolving technology that uses artificial intelligence (AI). It […]
10 Most Common Smart Home Issues (and How to Fix Them)
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators and voice-activated lights. But even the most advanced technology can have analog […]
What Is Microsoft Security Copilot? Should You Use It?
It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts of data. As well as respond to incidents quickly and effectively. Managing an organization’s security posture is complex. That’s where Microsoft Security Copilot comes in. Microsoft Security Copilot is a generative AI-powered security solution. It provides […]
Smart Tactics to Reduce Cloud Waste at Your Business
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste. Cloud waste is the unnecessary spending of resources and money on cloud services. These services are often not fully utilized or optimized. About 32% of cloud spending is wasted. This can […]
Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that lurk in the online world. Often, it’s our own actions that leave us most at risk of a cyberattack or online scam. Risky behaviors include weak passwords and lax security […]
Be Careful When Scanning QR Codes – There’s a New Scam Going Around!
QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are convenient and easy to use. You just scan them with your smartphone camera. You’re then directed to a link, a coupon, a video, or some other online content. With the […]
Workspaces, a VPN & More – Learn the Newest Microsoft Edge Features
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation. The latest updates bring a host of features. These are designed to enhance productivity, security, and browsing satisfaction. Chrome may have been number one for years. But Edge has been steadily gaining popularity. It is now the third most popular […]
These 7 AI Trends Are Sweeping the Cybersecurity Realm
Relentless digital innovation has defined the last few years. The symbiotic relationship between AI and cybersecurity has become pivotal especially when it comes to safeguarding sensitive information and digital assets. As cyber threats evolve in complexity, AI has emerged as a formidable ally. It empowers organizations with advanced tools and techniques. Helping them to stay […]
Online Security: Addressing the Dangers of Browser Extensions
Browser extensions have become as common as mobile apps. People tend to download many and use few. There are over 176,000 browser extensions available on Google Chrome alone. These extensions offer users extra functionalities and customization options. While browser extensions enhance the browsing experience, they also pose a danger which can mean significant risks to […]
How Small Businesses Are Unlocking Growth With Generative AI
Staying ahead in business often means embracing cutting-edge technologies. New tools can unlock new avenues for growth especially for small businesses. SMBs are often looking for affordable ways to gain a competitive advantage. One such transformative force is Generative Artificial Intelligence (GenAI). This is a technology that goes beyond automation and the AI we used […]
Examples of How a Data Breach Can Cost Your Business for Years
In the digital age, data is the lifeblood of businesses. It fuels operations, decision-making, and customer interactions. But there is a dark underbelly of this data-centric landscape. It’s the persistent threat of data breaches. The repercussions of a data breach extend far beyond the immediate aftermath. They often haunt businesses for years. Only 51% of […]
Are Your Smart Home Devices Spying On You? (Experts Say, Yes!)
The integration of smart home devices has become synonymous with modern living. They offer convenience, efficiency, and connectivity at our fingertips. But a recent study has raised concerns about the darker side of these smart gadgets. It suggests that our beloved smart home devices may be spying on us. It’s natural these days to invite […]
5 Ways to Leverage Microsoft 365’s New AI Innovations
Microsoft 365 has a powerful suite of cloud-based productivity tools. They can help you work smarter and faster. Microsoft has consistently been at the forefront of innovation. M365 was one of the very first all-in-one cloud tools, introduced as Office 365 in 2013. Now, Microsoft and its business tools are at the leading edge of […]
9 Tips for Setting Up AI Rules for Your Staff
Artificial intelligence (AI) is a powerful tool. It can enhance the productivity, efficiency, and creativity of your staff. But AI also comes with some challenges and risks. Businesses need to address and manage these to use AI effectively. Establishing clear and ethical guidelines, or “AI rules,” for staff interaction is essential. Otherwise, you may not […]
Gamers Beware! Hackers are Targeting You.
Gamers haven’t really been the focus of cybersecurity for a long time. You mostly hear about attacks on businesses. Or stolen personal data due to phishing attacks. But gamers are not safe from hackers targeting them. As cyberattacks continue to escalate, gamers have become prime hacking targets. Malicious actors seek to exploit vulnerabilities in the […]
How Small Businesses Can Approach Workforce Technology Modernization
Technology plays a pivotal role in driving efficiency, productivity, and competitiveness. For small businesses, workforce technology modernization is both an opportunity and a challenge. Embracing modern technology can empower small businesses. It can help them thrive in a digital era. Yet many of them don’t keep up with modernization. For example, over 30% of small […]
Need to Show the Tangible Value of Cybersecurity? Here’s How
You cannot overstate the importance of cybersecurity. Especially in an era dominated by digital advancements. Businesses and organizations are increasingly reliant on technology to drive operations. This makes them more susceptible to cyber threats. 66% of small businesses are concerned about cybersecurity risk. Forty-seven percent lack the understanding to protect themselves. This leaves them vulnerable […]
Top Data Breaches of 2023: Numbers Hit an All-Time High
The battle against cyber threats is an ongoing challenge. Unfortunately, 2023 has proven to be a watershed year for data breaches. Data compromises have surged to an all-time high in the U.S. This is based on data from the first 9 months of the year. Meaning that numbers will only end up higher for the […]
How Could Your Business Be Impacted by the New SEC Cybersecurity Requirements?
Cybersecurity has become paramount for businesses across the globe. As technology advances, so do the threats. Recognizing this, the U.S. Securities and Exchange Commission (SEC) has introduced new rules. They revolve around cybersecurity. These new requirements are set to significantly impact businesses. These rules are a response to the growing sophistication of cyber threats. As […]
How Can You Leverage the New MS Teams Payment App?
Are you a small business owner or a freelancer who offers services online? If so, you might be wondering how to get paid by your customers in a fast and convenient way. You might have tried different payment platforms. But they often require you to switch between different apps or websites. This can be time-consuming […]
Beware of These 2024 Emerging Technology Threats
The global cost of a data breach last year was USD $4.45 million. This is an increase of 15% over three years. As we step into 2024, it’s crucial to be aware of emerging technology threats. Ones that could potentially disrupt and harm your business. Technology is evolving at a rapid pace. It’s bringing new […]
14 Helpful Tips for New Year Digital Decluttering
These days, our lives are intricately woven into the digital fabric. From emails to photos, documents to apps, our devices store tons of information. It’s easy to feel overwhelmed at the sight of an endless inbox or app library. As the new year begins, it’s the perfect time for a digital declutter. A clean and […]
11 Ways to Responsibly Get Rid of E-Waste at Your Home or Office
In our tech-driven world, electronic devices have become indispensable. But with constant upgrades, what happens to the old gadgets? They tend to pile up and eat up storage space. But you can’t just throw them in the trash. E-waste poses a significant environmental threat if not disposed of responsibly. E-waste is a term that refers […]
7 Transformative Technology Trends Changing the Way We Work
Technology is reshaping the world of work at an unprecedented pace. From artificial intelligence to web3, from the metaverse to the hybrid work model. We are witnessing a series of technological revolutions. They are transforming how we communicate, collaborate, create, and innovate. Let’s explore some of the most impactful technology trends that are changing the […]
What Is the Most Secure Way to Share Passwords with Employees?
Breached or stolen passwords are the bane of any organization’s cybersecurity. Passwords cause over 80% of data breaches. Hackers get in using stolen, weak, or reused (and easily breached) passwords. But passwords are a part of life. Technologies like biometrics or passkeys haven’t yet replaced them. We use them for websites, apps, and more. So, […]
How to Organize Your Cybersecurity Strategy into Left and Right of Boom
In the pulsating digital landscape, every click and keystroke echoes through cyberspace. The battle for data security rages on. Businesses stand as both guardians and targets. Unseen adversaries covet their digital assets. To navigate this treacherous terrain takes a two-pronged approach. Businesses must arm themselves with a sophisticated arsenal of cybersecurity strategies. On one side, […]
Coolest Smart Gadgets at Europe’s Biggest Tech Trade Show (IFA)
Every year, tech enthusiasts eagerly anticipate Europe’s most prominent technology trade show. It’s the Internationale Funkausstellung Berlin, or simply IFA. This is a showcase of the latest and greatest innovations in consumer electronics. The show includes everything from cutting-edge smartphones to futuristic smart home gadgets. IFA never fails to impress. Let’s take a closer look […]
Choose Wisely: What Smart Home Tech Should You Adopt and Avoid?
In the age of smart living, our homes are becoming increasingly intelligent. They’re designed to cater to our every need. Smart gadgets are transforming how we turn on the lights, home security, and more. They even help us feed our pets from afar. But with the rapid evolution of this technology, it’s crucial to make […]
What Is SaaS Ransomware & How Can You Defend Against It?
Software-as-a-Service (SaaS) has revolutionized the way businesses operate. It offers convenience, scalability, and efficiency. No more dragging software from one device to another. Everyone can collaborate easily in the cloud. But alongside its benefits, SaaS brings with it potential threats. When software and data are online, they’re more vulnerable to attacks. One of the latest […]
Should Your Business Upgrade to the New Microsoft Intune Suite?
Endpoint management has changed a lot over the last two decades. There was a time when companies housed all endpoints in the same place. This made managing them simpler. But it held offices back from being mobile and flexible. Today’s office can include endpoints around the globe. Remote teams can work from anywhere. And people […]
Handy Tips to Optimize a Dual-Monitor Setup for the Best Experience
Two monitors are often better than one when it comes to getting things done efficiently. A dual-monitor setup can significantly enhance your productivity. This is true whether you’re a gamer, a creative professional, or an office wiz who loves to multitask. A study by Jon Peddie Research found that dual displays can increase productivity by […]
Does Your Business Have Any “Cybersecurity Skeletons” in the Closet?”
Let’s dive into a topic that might give you the chills—cybersecurity skeletons in the closet. You may not have old skeletons hidden away in the basement. But there’s a good chance of cybersecurity vulnerabilities lurking in the shadows. Just waiting to wreak havoc. You can’t fix what you can’t see. It’s time to shine a […]
Cybersecurity Awareness Month: Strengthening Your Team’s Defense with Essential Cyber Hygiene
As technology continues to advance, so does the need for heightened awareness. As well as proactive measures to safeguard sensitive information. Cybersecurity can seem like an insurmountable task for everyday people. But it’s not only a job for the IT team. Everyone can play a part in keeping their organization’s data safe. Not to mention […]
9 Reasons to Use Airplane Mode Even If You’re Not Traveling
Most people are familiar with their device’s Airplane Mode. You’ve probably used it when jetting off to exotic locations. But did you know that it’s not just for globetrotters? That’s right! Airplane Mode isn’t only for flying; it can be a handy feature for your everyday life. Here are some top reasons why you should […]
What Should You Expect in the New iOS 17?
Apple’s iOS updates have always been eagerly anticipated. iPhone and iPad users around the world get excited to see what their devices can do next. The newest major upcoming release will be for iOS 17. This fall, Apple is set to introduce a host of exciting new features and improvements. iOS 17 promises to deliver […]
These Technologies Can Help You Run Your Small Business Better
Running a small business can be challenging. But advancements in technology have opened a world of opportunities. Small business owners can use digital tools to streamline operations. As well as improve efficiency, and boost productivity. From innovative software to cutting-edge hardware, there are a lot of tools to choose from. The right technology can help […]
These 5 Small Business Tech Trends Can Fuel Your Growth
In today’s ever-evolving digital landscape, small businesses have more opportunities than ever. Many of these call for leveraging technology to their advantage. Embracing the right tech trends can help businesses compete. It enables them to streamline operations, enhance customer experiences, and fuel growth. But it can be confusing knowing which routes to take. Most small […]
Learn How to Spot Fake LinkedIn Sales Bots
LinkedIn has become an invaluable platform for professionals. People use it to connect, network, and explore business opportunities. But with its growing popularity have come some red flags. There has been an increase in the presence of fake LinkedIn sales bots. These bots impersonate real users and attempt to scam unsuspecting individuals. This is one […]
Have You Tried Out Microsoft Designer Yet? (Get the Scoop Here)
As technology continues to advance, so does the landscape of design tools. Microsoft has been a company at the forefront of business apps. Microsoft 365 began with about seven apps. It now offers new users access to over 20. One of the newest ones added is Microsoft Designer. This quick-and-easy design tool has caught the […]
6 Reasons Access Management Has Become a Critical Part of Cybersecurity
Cybersecurity has become paramount for businesses and individuals alike. Cyber threats abound, and data breaches and malware attacks are costly. Attacks come from all sectors, including the cloud tools you use every day. The average employee uses 36 cloud-based services daily. Managing access to sensitive data and resources has become crucial. It’s a vital piece […]
What is Zero-Click Malware? How Do You Fight It?
In today’s digital landscape, cybersecurity threats continue to evolve. They pose significant risks to individuals and organizations alike. One such threat gaining prominence is zero-click malware. This insidious form of malware requires no user interaction. It can silently compromise devices and networks. One example of this type of attack happened due to a missed call. […]
Top 7 Cybersecurity Risks of Remote Work & How to Address Them
Remote work has become increasingly popular in recent times. It provides flexibility and convenience for employees. Additionally, telecommuting reduces office costs for employers. Many also cite productivity benefits due to fewer distractions. Research shows a 56% reduction in unproductive time when working at home vs. the office. But there are some drawbacks to working outside […]
Handy Checklist for Handling Technology Safely During a Home or Office Move
Moving can be a chaotic and stressful time. Especially when it comes to handling your valuable technology. Whether you’re relocating your home or office, it’s essential to take extra care. Both with fragile items and when packing and moving your devices and other tech items. To help you navigate this process smoothly, we’ve put together […]
Do You Still Believe in These Common Tech Myths?
In today’s digital age, technology plays a significant role in our lives. But along with the rapid advancements and innovations, several myths have persisted. Is it okay to leave your smartphone charging overnight? Do Macs get viruses? And what about those 5G towers? What’s going on with those? Common tech myths can often lead to […]
7 Advantages of Adopting a Defense-in-Depth Cybersecurity Strategy
Cybersecurity threats are becoming increasingly sophisticated and prevalent. In 2022, ransomware attacks jumped by 93%. The introduction of ChatGPT will only increase the potential damage of cyber-attacks. Protecting sensitive data and systems requires a comprehensive approach. One that goes beyond a single security solution. This is where a defense-in-depth cybersecurity strategy comes into play. In […]
Is Your Online Shopping App Invading Your Privacy?
Online shopping has become a common activity for many people. It’s convenient, easy, and allows us to buy items from the comfort of our homes. But with the rise of online shopping, there are concerns about privacy and security. Not all shopping apps are created equally. Often people get excited and install an app without […]
How to Use Threat Modeling to Reduce Your Cybersecurity Risk
As cyber threats continue to increase, businesses must take proactive steps. They need to protect their sensitive data and assets from cybercriminals. Threats to data security are persistent and they come from many different places. Today’s offices are digitally sophisticated. Just about every activity relies on some type of technology and data sharing. Hackers can […]
Business Email Compromise Jumped 81% Last Year! Learn How to Fight It
In recent years, electronic mail (email for short) has become an essential part of our daily lives. Many people use it for various purposes, including business transactions. With the increasing dependence on digital technology, cybercrime has grown. A significant cyber threat facing businesses today is Business Email Compromise (BEC). Why is it important to pay […]
10 Tips to Help Small Businesses Get Ready for the Unexpected
What would you do if your business suffered a ransomware attack tomorrow? Do you have a contingency plan in case of a tornado, hurricane, or earthquake? The unexpected can happen anytime, and small businesses can get hit particularly hard. Small businesses are the backbone of many economies. They are critical for job creation, innovation, and […]
9 NSA Best Practices for Securing Your Home Network
In today’s world, technology is ubiquitous, and connectivity is a must. Securing your home network has become more critical than ever. A secure home network is essential for protecting your personal data from hackers. From phishing to smishing (SMS phishing), it’s getting harder to avoid a breach. Individuals often have fewer safeguards in place at […]
What Is Push-Bombing & How Can You Prevent It?
Cloud account takeover has become a major problem for organizations. Think about how much work your company does that requires a username and password. Employees end up having to log into many different systems or cloud apps. Hackers use various methods to get those login credentials. The goal is to gain access to business data […]
Is It Time to Ditch the Passwords for More Secure Passkeys?
Passwords are the most used method of authentication, but they are also one of the weakest. Passwords are often easy to guess or steal. Also, many people use the same password across several accounts. This makes them vulnerable to cyber-attacks. The sheer volume of passwords that people need to remember is large. This leads to […]
How to Create Insightful Dashboards in Microsoft Power BI
Data visualization is a powerful tool for communicating complex data. It presents it in a simple, easily understandable format. But it is not enough to simply create a graph or chart and call it a day. To truly make use of information, it is important to create insightful reports. Reports that effectively communicate the story […]
Best Ways to Use ChatGPT at Your Business (Without Things Getting Out of Hand)
It’s hard to turn around online these days without running into ChatGPT. Both Bing and Google are levering this advanced artificial intelligence language model. And you can expect it to show up in more business and personal tools that you use every day. ChatGPT has revolutionized the way businesses interact with their customers. It has […]
7 Smart Ways to Secure Your Wireless Printer & Keep Your Home Network Safe
Many people worry about someone hacking their computer. But they’re not really thinking about their wireless printer getting breached. It’s a tool that most individuals use sporadically. For example, when you want to print out tax forms or mailing labels. Printers tend to be out of sight, out of mind. That is until you need […]
6 Immediate Steps You Should Take If Your Netflix Account is Hacked
Netflix is one of the most popular and well-known streaming services. It has nearly 231 million subscribers around the world. It has been growing steadily for almost a decade. The platform has become an essential part of many people’s daily entertainment routines. They fire up their devices, log in, and pick right back up on […]
What Is App Fatigue & Why Is It a Security Issue?
The number of apps and web tools that employees use on a regular basis continues to increase. Most departments have about 40-60 different digital tools that they use. 71% of employees feel they use so many apps that it makes work more complex. Many of the apps that we use every day have various alerts. […]
These Everyday Objects Can Lead to Identity Theft
You wouldn’t think a child’s toy could lead to a breach of your personal data. But this happens all the time. What about your trash can sitting outside? Is it a treasure trove for an identity thief trolling the neighborhood at night? Many everyday objects can lead to identity theft. They often get overlooked because […]
How to Use the New Virtual Appointments in Microsoft Teams
Scheduling appointments is a common activity. Salespeople often set up virtual appointments to answer questions about a product. Software companies allow people to schedule live demos. Telehealth therapists allow clients to book video sessions. Those are just a few examples of some groups that are going to love a new Microsoft Teams feature. Virtual Appointments […]
7 Customer-Facing Technologies to Give You an Advantage
Customers look for convenience. In today’s world that means technology that makes their life easier. From webforms to POS systems, you need to keep the customer experience in mind in all you do. When people aren’t happy with their experience interacting with a company, they leave. And their experience might not have anything to do […]
6 Things You Should Do to Handle Data Privacy Updates
Once data began going digital, authorities realized a need to protect it. Thus, the creation of data privacy rules and regulations to address cyber threats. Many organizations have one or more data privacy policies they need to meet. Those in the U.S. healthcare industry and their service partners need to comply with HIPAA. Anyone collecting […]
Why You Need to Think Twice Before Using Lensa AI & Other Self-Portrait Apps
It’s a common theme. You begin seeing these amazing CGI images of your friends on Facebook or Instagram. You think, “How can I make one?” Filters and self-portrait apps have come a long way. You can now make yourself look like Hollywood’s version of a character in the next hit animated film. It still kind […]
Microsoft Forms: One of the Handiest Freebies in Microsoft 365
Microsoft 365 is one of the most popular cloud platforms in the world, with about 345 million paid seats. Microsoft cloud tools numbers were up 32% in Q3 2022 compared to the previous year. One of the reasons for its continued growth is the suite of cloud tools offered in the service. Users get a […]
Data Backup Is Not Enough, You Also Need Data Protection
The need to back up data has been around since floppy disks. Data loss happens due to viruses, hard drive crashes, and other mishaps. Most people using any type of technology have experienced data loss at least once. There are about 140,000 hard drive crashes in the US weekly. Every five years, 20% of SMBs […]
8 Reasons Every Company Is Now a Technology Company
Whether you sell shoes or run an accounting firm, you need some type of technology to operate. Today’s companies aren’t just in the business of selling their own goods and services anymore. They also must master various types of digital tools. These include software, payment systems, computers, Wi-Fi networks, mobile devices, and more. Companies also […]
6 Steps to Effective Vulnerability Management for Your Technology
Technology vulnerabilities are an unfortunate side effect of innovation. When software companies push new updates, there are often weaknesses in the code. Hackers exploit these. Software makers then address the vulnerabilities with a security patch. The cycle continues with each new software or hardware update. It’s estimated that about 93% of corporate networks are susceptible […]
Is That Really a Text from Your CEO… or Is It a Scam?
Imagine you’re going about your day when suddenly you receive a text from the CEO. The head of the company is asking for your help. They’re out doing customer visits and someone else dropped the ball in providing gift cards. The CEO needs you to buy six $200 gift cards and text the information right […]
6 Ways to Prevent Misconfiguration (the Main Cause of Cloud Breaches)
Misconfiguration of cloud solutions is often overlooked when companies plan cybersecurity strategies. Cloud apps are typically quick and easy to sign up for. The user often assumes that they don’t need to worry about security because it’s handled. This is an incorrect assumption because cloud security is a shared model. The provider of the solution […]
The Pros & Cons of Tracking Your Employees’ Every Digital Movement
Since the pandemic, employers around the world have needed to change. They’ve had to shift how their employees operate. Remote work is very much here to stay. Organizations and employees can both benefit from the work-from-home and hybrid work revolution. Cost savings is a driver for supporting remote work. Employee morale and productivity also can […]
Smart Tips to Stop Money From Being Stolen Through Online Banking
There are a lot of things that have changed since the invention of the internet. One of these is how we bank and access our accounts. You used to have to go into a local bank branch to make deposits and withdrawals. Now, you can take a picture of a check and deposit it from […]
Cool Windows 11 Features That May Make You Love This OS
Microsoft released the Windows 11 operating system (OS) over a year ago. It was largely well-received as stable and user-friendly. The OS is not a large departure from the Windows 10 experience. But it does offer a lot of enhancements over the older environment. Yet with several improvements and a free upgrade for Windows 10 […]
4 Proven Ways to Mitigate the Costs of a Data Breach
No business wants to suffer a data breach. But unfortunately, in today’s environment, it’s difficult to completely avoid them. Approximately 83% of organizations have experienced more than one data breach. (IBM Security 2022 Cost of a Data Breach Report) These breaches hurt businesses in many ways. First, there is the immediate cost of remediating the […]
Mobile Malware Has Increased 500% – What Should You Do?
Cybersecurity researchers uncovered an alarming mobile statistic. During the first few months of 2022, mobile malware attacks surged by 500%. This is alarming both in scale and because many people aren’t yet protecting smartphones. For years, mobile phones have become more powerful. They now do many of the same functions as a computer – just […]
Have You Had Data Exposed in One of These Recent Data Breaches
There’s a reason that browsers like Edge have added breached password notifications. Data breaches are an unfortunate part of life. And can have costly consequences for individuals. Hackers can steal identities and compromise bank accounts, just to name a couple. Cybercriminals breach about 4,800 websites every month with form jacking code. It has become all […]
2023 Trends in Data Privacy That Could Impact Your Compliance
Data privacy has been a growing requirement ever since the internet age began. So much personal information is flying around through computer networks. Protecting it has become a mandate. Most companies must follow HIPAA, GDPR, or another industry or locality-based privacy rule. By the end of 2024, 75% of the world’s population will have their […]
8 Tech Checks to Make Before You Travel
Our technology inevitably comes with us when we travel. Most of us won’t even travel to the end of the block without our smartphones. When you go on a trip, not having your technology there when you need it can ruin your day. Travel smarter and more securely by doing several checks before you go. […]
What’s Changing in the Cybersecurity Insurance Market?
Cybersecurity insurance is still a pretty new concept for many SMBs. It was initially introduced in the 1990s to provide coverage for large enterprises. It covered things like data processing errors and online media. Since that time, the policies for this type of liability coverage have changed. Today’s cyber insurance policies cover the typical costs […]
What Cybersecurity Attack Trends Should You Watch Out for in 2023?
The new year has just begun and it’s a time of renewal as we plan for the possibilities to come in 2023. It’s also a time when you need to plan for resiliency in the face of ever-present cyberattacks. Sixty-eight percent of surveyed business leaders feel that cybersecurity risks are getting worse. They have a […]
Don’t Set Yourself Up to Fail: Tips for Safer Home Security Setups
The global home security market has been growing by leaps and bounds. By 2026, experts expect the market to expand at a rate of 20.1%. This is on top of an expected increase of 21.6% from 2021 to 2022. From Ring doorbell cams to entire home security systems, consumers want these solutions. Watching your front […]
Align Your Team to Company Targets with Microsoft Viva Goals
You often hear the words “digital transformation” and “collaboration.” But what do they actually mean? What do they mean for the day-to-day of running your business? Collaboration can’t happen without shared goals. When departments are siloed and unconnected, priorities can conflict. People are doing their best but may not be moving in the same direction. […]
7 VoIP Setup Tips for a More Productive Office
The global pandemic put a big emphasis on the need to run a business from anywhere. Enabling employees to work remotely requires cloud solutions. This includes collaborative platforms like Google Workspace and Microsoft 365. VoIP (Voice over Internet Protocol) phone systems have also become critical. VoIP allows companies to stay in contact with customers and […]
5 Ways to Balance User Productivity with Solid Authentication Protocols
One constant struggle in offices is the balance between productivity and security. If you give users too much freedom in your network, risk increases. But add too many security gates, and productivity can dwindle. It’s a fine balance between the two, but one you can achieve. Organizations need to recognize the importance of both. And […]
What to Include in a Year-end Technology Infrastructure Review
When the year is coming to a close, it’s the perfect time to plan for the future. Most businesses begin the year with the hope of growing and improving operations. Much of how a business operates depends on technology. So, it makes sense to look to your IT for areas of optimization. A year-end technology […]
What Are the Advantages of Implementing Conditional Access?
It seems that nearly as long as passwords have been around, they’ve been a major source of security concern. Eighty-one percent of security incidents happen due to stolen or weak passwords. Additionally, employees continue to neglect the basics of good cyber hygiene. For example, 61% of workers use the same password for multiple platforms. And […]
Tips for Overcoming Barriers to a Smooth BYOD Program
Bring your own device (BYOD) is a concept that took hold after the invention of the smartphone. When phones got smarter, software developers began creating apps for those phones. Over time, mobile device use has overtaken desktop use at work. According to Microsoft, mobile devices make up about 60% of the endpoints in a company […]
Simple Setup Checklist for Microsoft Teams
Microsoft Teams is a lot of things. It’s a video conferencing tool, a team messaging channel, and a tool for in-app co-authoring, just to name a few. During the pandemic, the popularity of Teams skyrocketed. User numbers for MS Teams jumped from 20 million in November 2019 to 75 million in April 2020. As of […]
7 Things to Consider When Getting a New Computer to Avoid Buyer’s Remorse
Have you ever bought a new computer and then had buyer’s remorse a few months later? Maybe you didn’t pay attention to the storage capacity and ran out of space. Or you may have glossed over memory and experienced constant freeze-ups. An investment in a new PC isn’t something you want to do lightly. Doing […]
7 Apps That Can Help You Improve Customer Experience in 2023
Paying attention to your customer experience directly impacts your bottom line. Companies that are “customer-centric” are 60% more profitable than those that aren’t. In this digital age, customers also expect more from those they do business with. In today’s world, people can order something on their phones and see it on their doorstep the next […]
What Are the Most Helpful VoIP Features for Small Businesses?
Just five or six years ago, VoIP was still considered a “different” type of business phone system. One that wasn’t the norm. But the pandemic changed that way of thinking. Now internet-based phone systems aren’t simply the norm. They’re mandatory for business continuity. During the pandemic, VoIP and video conferencing have skyrocketed by over 210%. […]
Simple Guide to Follow for Better Endpoint Protection
Endpoints make up much of a company’s network and IT infrastructure. This is a collection of computers, mobile devices, servers, and smart gadgets. As well as other IoT devices that all connect to the company network. The number of endpoints a company has will vary by business size. Companies with less than 50 employees have […]
Insider Threats Are Getting More Dangerous! Here’s How to Stop Them
One of the most difficult types of attacks to detect are those performed by insiders. An “insider” would be anyone that has legitimate access to your company network and data. This would be via a login or other authorized connection. Because insiders have authorized system access, they bypass certain security defenses. Such as those designed […]
Everything You Need to Know About Microsoft Viva Sales
Data entry can be a real drag for salespeople. The time they spend on administrative tasks is time away from customer interactions. But that data is vital. It’s important to capture customer orders, quotes, needs, and more. Lead and sales reporting help sales managers know where to direct their attention. Analytics also help drive more […]
Checklist for Better Digital Offboarding of Employees
Digital footprints cover today’s modern workplace. Employees begin making these the moment they’re hired. They get a company email address and application logins. They may even update their LinkedIn page to connect to your company. When an employee leaves a company, there is a process that needs to happen. This is the process of “decoupling” […]
9 Urgent Security Tips for Online Holiday Shopping
The holiday shopping season is taking off. This means that scammers have also revved up their engines. They’re primed and ready to take advantage of all those online transactions. Don’t forget to stay safe online during the buying frenzy that occurs this time of year. An ounce of cybersecurity prevention is definitely worth a pound […]
7 Pro Tips for Microsoft 365
Microsoft 365 is the most popular of all major office productivity software. It has 48.8% of the global market share, just edging out Google’s apps, by a couple of percentage points. It’s used by individuals, small & mid-sized businesses, and larger enterprise organizations. It does everything a modern office needs. Including from word processing and […]
What Is Microsoft Defender for Individuals & What Does It Do?
When you hear about Microsoft adding security apps to M365, it’s often the business versions. But the pandemic has changed the way that we see the workplace. It’s now a hybrid world. One made up of several connected “mini-offices” located in employee homes. The outsourcing market has also contributed to the change in company networks. […]
The Biggest Vulnerabilities that Hackers are Feasting on Right Now
Software vulnerabilities are an unfortunate part of working with technology. A developer puts out a software release with millions of lines of code. Then, hackers look for loopholes that allow them to breach a system through that code. The developer issues a patch to fix the vulnerability. But it’s not long before a new feature […]
You Need to Watch Out for Reply-Chain Phishing Attacks
Phishing. It seems you can’t read an article on cybersecurity without it coming up. That’s because phishing is still the number one delivery vehicle for cyberattacks. A cybercriminal may want to steal employee login credentials. Or wish to launch a ransomware attack for a payout. Or possibly plant spyware to steal sensitive info. Sending a […]
What Should You Do to Reduce Risk When Your Mobile Device Goes Missing?
Few things invoke instant panic like a missing smartphone or laptop. These devices hold a good part of our lives. This includes files, personal financials, apps, passwords, pictures, videos, and so much more. The information they hold is more personal than even that which is in your wallet. It’s because of all your digital footprints. […]
Microsoft Productivity Score Overview
Productivity can be challenging to track, no matter where employees are working. How do you know they’re using their tools as effectively as possible? How can you enable them to adopt best practices? These are questions that managers often ask themselves. If they’re looking at the wrong things, it can get in the way of […]
Helpful Tips for Keeping Your Shared Cloud Storage Organized
Cloud file storage revolutionized the way we handle documents. No more having to email files back and forth. No more wondering which person in the office has the most recent copy of a document. Between 2015 and 2022, the percentage of worldwide corporate data stored in the cloud doubled. It went from 30% to 60%. […]
6 Important IT Policies Any Size Company Should Implement
Many small businesses make the mistake of skipping policies. They feel that things don’t need to be so formal. They’ll just tell staff what’s expected when it comes up and think that’s good enough. But this way of thinking can cause issues for small and mid-sized business owners. Employees aren’t mind readers. Things that you […]
6 Discontinued Technology Tools You Should Not Be Using Any Longer
One constant about technology is that it changes rapidly. Tools that were once staples, like Internet Explorer and Adobe Flash, age out. New tools replace those that are obsolete. Discontinued technology can leave computers and networks vulnerable to attacks. While older technology may still run fine on your systems that doesn’t mean that it’s okay […]
How Using the SLAM Method Can Improve Phishing Detection
There is a reason why phishing is usually at the top of the list for security awareness training. For the last decade or two, it has been the main delivery method for all types of attacks. Ransomware, credential theft, database breaches, and more launch via a phishing email. Why has phishing remained such a large […]
Did You Just Receive a Text from Yourself? Learn What Smishing Scams to Expect
How many text messages from companies do you receive today as compared to about two years ago? If you’re like many people, it’s quite a few more. This is because retailers have begun bypassing bloated email inboxes. They are urging consumers to sign up for SMS alerts for shipment tracking and sale notices. The medical […]
How Often Do You Need to Train Employees on Cybersecurity Awareness?
You’ve completed your annual phishing training. This includes teaching employees how to spot phishing emails. You’re feeling good about it. That is until about 5-6 months later. Your company suffers a costly ransomware infection due to a click on a phishing link. You wonder why you seem to need to train on the same information […]
Home Security: Why You Should Put IoT Devices on a Guest Wi-Fi Network
The number of internet-connected devices in homes has been growing. It’s increased exponentially over the last decade. A typical home now has 10.37 devices connected to the internet. PCs and mobile devices make up a little over half of those and the rest are IoT devices. IoT stands for Internet of Things. It means any […]
Get More Unplugged Laptop Time with These Battery-Saving Hacks
One of the big draws of a laptop computer is that you can use it anywhere. You don’t need to have it plugged in all the time because it has an internal battery. Your laptop may start out with several hours of battery life when you first buy it. But the lifespan can get shorter […]
Microsoft Productivity Score Overview
Posted On July 20, 2022 Productivity can be challenging to track, no matter where employees are working. How do you know they’re using their tools as effectively as possible? How can you enable them to adopt best practices? These are questions that managers often ask themselves. If they’re looking at the wrong things, it can get […]
6 Discontinued Technology Tools You Should Not Be Using Any Longer
Posted On July 20, 2022 One constant about technology is that it changes rapidly. Tools that were once staples, like Internet Explorer and Adobe Flash, age out. New tools replace those that are obsolete. Discontinued technology can leave computers and networks vulnerable to attacks. While older technology may still run fine on your systems that doesn’t […]
6 Important IT Policies Any Size Company Should Implement
Posted On July 20, 2022 Many small businesses make the mistake of skipping policies. They feel that things don’t need to be so formal. They’ll just tell staff what’s expected when it comes up and think that’s good enough. But this way of thinking can cause issues for small and mid-sized business owners. Employees aren’t mind […]
What Should You Do to Reduce Risk When Your Mobile Device Goes Missing?
Posted On July 20, 2022 Few things invoke instant panic like a missing smartphone or laptop. These devices hold a good part of our lives. This includes files, personal financials, apps, passwords, pictures, videos, and so much more. The information they hold is more personal than even that which is in your wallet. It’s because of […]
Helpful Tips for Keeping Your Shared Cloud Storage Organized
Posted On July 20, 2022 Cloud file storage revolutionized the way we handle documents. No more having to email files back and forth. No more wondering which person in the office has the most recent copy of a document. Between 2015 and 2022, the percentage of worldwide corporate data stored in the cloud doubled. It went […]
5 Exciting Ways Microsoft 365 Can Enable the Hybrid Office
Posted On June 23, 2022 “Hybrid office” is the new buzzword you’ll hear used in business discussions. It’s the mix of having employees both working at the office and working from home. This has become more than a buzzword and is now the reality for many companies. There was a survey of employees with remote-capable jobs. […]
5 Exciting Ways Microsoft 365 Can Enable the Hybrid Office
Posted On June 23, 2022 “Hybrid office” is the new buzzword you’ll hear used in business discussions. It’s the mix of having employees both working at the office and working from home. This has become more than a buzzword and is now the reality for many companies. There was a survey of employees with remote-capable jobs. […]
How Using the SLAM Method Can Improve Phishing Detection
Posted On June 23, 2022 There is a reason why phishing is usually at the top of the list for security awareness training. For the last decade or two, it has been the main delivery method for all types of attacks. Ransomware, credential theft, database breaches, and more launch via a phishing email. Why has phishing […]
Did You Just Receive a Text from Yourself? Learn What Smishing Scams to Expect
Posted On June 23, 2022 How many text messages from companies do you receive today as compared to about two years ago? If you’re like many people, it’s quite a few more. This is because retailers have begun bypassing bloated email inboxes. They are urging consumers to sign up for SMS alerts for shipment tracking and […]
How Often Do You Need to Train Employees on Cybersecurity Awareness?
Posted On June 23, 2022 You’ve completed your annual phishing training. This includes teaching employees how to spot phishing emails. You’re feeling good about it. That is until about 5-6 months later. Your company suffers a costly ransomware infection due to a click on a phishing link. You wonder why you seem to need to train […]
Are Two Monitors Really More Productive Than One?
Posted On May 18, 2022 When you see those people with two monitors, you may assume they do some specialized work that requires all that screen space, or they just really like technology. But having the additional display real estate that a second screen provides can benefit anyone, even if you’re doing accounting or document work […]
Pros & Cons of Using the Windows 365 Cloud PC
Posted On May 18, 2022 While many companies have moved most of their workflows to the cloud, there is still a key component of office operations that is location-based. This would be employee computers. Most companies still rely on desktops and laptops to allow employees to access critical software and as their main workstation. This can […]
Should I Consider Switching to Microsoft’s Edge Browser? (Top Features)
Posted On May 18, 2022 One of the most important applications we choose is our internet browser. When on a computer or a mobile device, we work in that most of the time because many applications are now cloud-based, so accessing them means going through your browser. Over the years browsers have come and gone. A […]
Signs That Your Computer May Be Infected with Malware
Posted On May 18, 2022 Approximately 34% of businesses take a week or longer to regain access to their data and systems once hit with a malware attack. Malware is an umbrella term that encompasses many different types of malicious code. It can include: Viruses Ransomware Spyware Trojans Adware Key loggers And more The longer that malware sits […]
Top 5 Mobile Device Attacks You Need to Watch Out For
Posted On May 18, 2022 Smartphones and tablets are often the preferred device for communications, web searching, and accessing many types of apps. They’re more portable and can be used from anywhere. We’re seeing the takeover of many activities that used to be performed on traditional computers. Now, people are using mobile devices instead. For example, […]
Which Form of MFA Is the Most Secure? Which Is the Most Convenient?
Posted On May 18, 2022 Credential theft is now at an all-time high and is responsible for more data breaches than any other type of attack. With data and business processes now largely cloud-based, a user’s password is the quickest and easiest way to conduct many different types of dangerous activities. Being logged in as a user (especially […]
What Are the Best Ways to Give an Older PC New Life?
Posted On April 28, 2022 Purchasing a new computer is a big investment. Many small businesses and home PC owners end up struggling with older systems because they want to get as many years out of them as possible. Have you found yourself banging on your keyboard in frustration? Have you tried every tip and trick […]
Microsoft Teams Plan Comparison: Free vs M365 Business vs Teams Essentials
Posted On April 28, 2022 The shift to remote work over the last two years has caused companies to realign their digital tools. Now, many meetings default to being via video conference rather than in person, and working from home has become commonplace. Seventy-seven percent of remote workers say they’re more productive working from home (a […]
What Are the Best Ways to Give an Older PC New Life?
Posted On April 28, 2022 Purchasing a new computer is a big investment. Many small businesses and home PC owners end up struggling with older systems because they want to get as many years out of them as possible. Have you found yourself banging on your keyboard in frustration? Have you tried every tip and trick […]
6 Ways to Combat Social Phishing Attacks
Posted On April 28, 2022 Phishing is the number one method of attack delivery for everything from ransomware to credential theft. We are very aware of it coming by email, but other types of phishing have been growing rapidly. In recent years, phishing over social media has skyrocketed by 500%. There has also been a 100% increase […]
How to Protect Your Online Accounts from Being Breached
Posted On April 28, 2022 Stolen login credentials are a hot commodity on the Dark Web. There’s a price for every type of account from online banking to social media. For example, hacked social media accounts will go for between $30 to $80 each. The rise in reliance on cloud services has caused a big increase in breached […]
What You Need to Know About the Rise in Supply Chain Cyberattacks
Posted On April 28, 2022 Any cyberattack is dangerous, but the particularly devastating ones are those on supply chain companies. These can be any supplier – digital or non-digital – of goods and services. We’ve seen several attacks on the supply chain occur in 2021 that had wide-reaching consequences. These are “one-to-many” attacks where victims can […]
4 Interesting Cloud Storage Trends to Watch for in 2022
Posted On April 28, 2022 One area of cloud computing that is used widely, but often isn’t as flashy as the software side is cloud storage. Storing files in the cloud to make them easily accessible and shareable from anywhere was one of the very first uses of the cloud that was adopted widely by many […]
4 Interesting Cloud Storage Trends to Watch for in 2022
Posted On April 28, 2022 One area of cloud computing that is used widely, but often isn’t as flashy as the software side is cloud storage. Storing files in the cloud to make them easily accessible and shareable from anywhere was one of the very first uses of the cloud that was adopted widely by many […]
5 Things You Should Never Do on a Work Computer
Posted On March 25, 2022 Whether you work remotely or in an office, the line between personal and work tasks can become blurred when working on your company computer. If you’re in front of a computer for most of your time during work, then it’s not unusual to get attached to your desktop PC. Over time, […]
Important Steps to Take Before You Recycle a Mobile Phone Number
Posted On March 25, 2022 It’s not unusual to change a mobile number from time to time. For example, when you move, you may want a number that is local to the area you just moved to. Companies also may end up recycling mobile numbers throughout their staff as people come and go. If you don’t […]
These Google Search Tips Will Save You Tons of Time!
Posted On March 21, 2022 Over 2.4 million searches happen every minute on Google. It’s often the first stop people make when they go online. We search daily for both personal and work needs, and often searching out the right information can take a lot of time if you have to sift through several irrelevant results. One study […]
What Are the Most Helpful Features of Windows 11?
Posted On March 21, 2022 Windows 11 has been out for a few months now, beginning rollout in October of 2021. It has been largely well-received and seen as stable with very few bugs noted. One of the reasons that Windows 11 has been welcomed with open arms for both home and business computer upgrades is that it […]
Top 5 Cybersecurity Mistakes That Leave Your Data at Risk
Posted On March 21, 2022 The global damage of cybercrime has risen to an average of $11 million USD per minute, which is a cost of $190,000 each second. 60% of small and mid-sized companies that have a data breach end up closing their doors within six months because they can’t afford the costs. The costs of falling […]
Alarming Phishing Attack Trends to Beware of in 2022
Posted On March 21, 2022 In 2020, 75% of companies around the world experienced a phishing attack. Phishing remains one of the biggest dangers to your business’s health and wellbeing because it’s the main delivery method for all types of cyberattacks. One phishing email can be responsible for a company succumbing to ransomware and having to face costly […]
The 7 Effective Features to Maximize Your Productivity on Google Drive
Posted On March 2, 2022 Google Drive is more than a file-sharing platform. It allows you to streamline your work in ways you never thought were possible. Learn how it can help boost workplace productivity. Did you know that something as simple as organizing your business is crucial to success? The truth is that dealing with […]
How OneNote Can Streamline Team Collaboration (And Four Tips to Make the Most of This Program)
Posted On March 2, 2022 OneNote is a digital note-taking tool that comes with plenty of benefits for users. But what you may not have realized yet is how powerful this app can be for enhancing team collaboration. Note-taking. This is an essential part of day-to-day operations for many business owners, managers, and teams. After all, […]
How OneNote Can Streamline Team Collaboration (And Four Tips to Make the Most of This Program)
Posted On March 2, 2022 OneNote is a digital note-taking tool that comes with plenty of benefits for users. But what you may not have realized yet is how powerful this app can be for enhancing team collaboration. Note-taking. This is an essential part of day-to-day operations for many business owners, managers, and teams. After all, […]
Why Protecting Your Printers from Cybercrime Is a Must (And 8 Tips for Improving Printer Security)
Posted On March 2, 2022 Printing devices are often overlooked when it comes to security. But the reality is, cybercriminals can hack your printer to get confidential information. Your printer is probably the last piece of computer equipment you thought needed protection from cybercriminals. But the truth is very different. Attackers actively try to locate the […]
Making Your VoIP Network Bulletproof (Six Tips to Protect Your VoIP from Cyberattacks)
Posted On March 2, 2022 Hardly any phone call system in a business beats VoIP when it comes to efficiency and flexibility. However, it’s not immune to cyberattacks. Discover how you can secure your VoIP ASAP. What kind of communication system are you using for your business? I asked because many modern-day businesses have now switched […]
The Critical Importance of Virtualized Infrastructure Security (And 4 Ways to Enhance It)
Posted On March 2, 2022 A torn-down virtual infrastructure creates risks for any business. And it can have a significant impact on how quickly you can retrieve your data and resume operations following an attack. These days, many businesses use virtualized infrastructure for more straightforward data storage. It’s because this approach is superior to physical solutions […]
Lead Your Business More Effectively by Implementing Unified Communications
Posted On March 2, 2022 Unified communications are a go-to solution for business owners looking to streamline their businesses and increase employee productivity in the long term. See how it benefits your business. Providing high-quality communication channels is crucial for any company. After all, it promotes cross-department collaboration and faster exchange of ideas. Since phones often […]
Timeless Methods of Improving Your Productivity – Here are 7 Things You Can Do to Be More Productive
Posted On January 30, 2022 Low productivity can be a massive obstacle to growing your business. Luckily, there are many ways to solve this problem. Many people struggle to finish the task at hand. No matter how long they’ve been in the business, productivity seems to evade them regularly. And this probably happens to you, too, […]
It’s No Internet Explorer – 7 Features of Microsoft Edge That Make the App a Productivity Powerhouse
Posted On January 29, 2022 Many business owners shy away from Microsoft Edge, thinking it’ll slow down their operations. However, the browser has been massively upgraded and can help boost productivity. Microsoft has made great strides since the introduction of Internet Explorer. The company now offers Microsoft Edge, a refined version that arguably provides the best […]
Is Updating From Windows 10 to 11 Worth It? Here Are the New Features in the OS (And Some Missing Ones)
Posted On January 29, 2022 Getting used to Windows 11 shouldn’t be too challenging. On the contrary, the OS comes with several intuitive features to enhance productivity. Microsoft recently introduced Windows 11 as the company’s latest operating system. And compared to Windows 10, this OS has various features that can increase your productivity and provide a […]
Which Type of Hacker Is Endangering Your Business Data? (And How to Protect Your Sensitive Info From Them)
Posted On January 29, 2022 Your data is pivotal to running a successful company. If you don’t have proper security measures in place, hackers can easily steal your data and take you out of business. Cybercriminals might be the biggest threat facing your company. Besides gaining access to your money and accounts, they can also take […]
Why Having a Continuity Plan Is a Sign of Great Leadership (And How to Create a Foolproof Plan)
Posted On January 29, 2022 Your business faces all sorts of threats that can disrupt your operations. A comprehensive continuity plan can help address them. Carrying on with business as usual is easy when nothing out of the ordinary is happening. But the fact is, crises can strike anytime. And when it happens, you need to […]
What Is an MSP (And How to Choose the Right One for Your Business)
Posted On January 29, 2022 Managing data and IT solutions in-house can be challenging and expensive. That’s why many organizations turn to MSPs. Digitalization has forced businesses to alter their operations and make IT a huge part of their day-to-day affairs. Still, some owners can’t cope with the change effectively, so they hire a managed service […]
Enhance Your Server Management with These 8 Tips
Posted On December 30, 2021 You may have state-of-the-art servers, but their efficiency can diminish over time. Managing them is key to optimizing your business operations. Numerous organizations rely on servers for various IT functions, such as applications, emails, hosting websites, and data storage. Although many companies have turned to cloud-based services using remote data centers, […]
Increasing Your Office Productivity With Streamlined Android Apps – The 3 Best Solutions
Posted On December 30, 2021 Is your team also using their Android mobile devices to do their tasks? Incorporating an Android suite of apps into your workplace can dramatically improve productivity. Many organizations opt for Android to take their office productivity to the next level. After all, they can provide higher flexibility, better workflows, and efficient […]
Enhancing Office Productivity With Google Chrome: The 12 Best Extensions To Improve Your Workflow
Posted On December 30, 2021 Working from your computer or smartphone is convenient, but it can also be distracting. To maintain productivity, you should install effective Google Chrome Extensions. Google Chrome is arguably the most popular browser on the planet. It’s best known for allowing faster loading of websites, optimized performance, and an intuitive interface. As […]
Enhance Your Server Management with These 8 Tips
Posted On December 30, 2021 You may have state-of-the-art servers, but their efficiency can diminish over time. Managing them is key to optimizing your business operations. Numerous organizations rely on servers for various IT functions, such as applications, emails, hosting websites, and data storage. Although many companies have turned to cloud-based services using remote data centers, […]
Improve Your Workplace Productivity With Microsoft Word: 11 Tips To Make the Most of This Program
Posted On December 30, 2021 Microsoft Word is an indispensable part of most business environments. It has numerous features that can help you boost productivity. Microsoft Word is one of the most popular office programs in the world. It allows millions of people to complete their duties more efficiently. Whether you’re a beginner or advanced user, […]
11 Effective Security Measures To Bolster Your Microsoft 365 Data Protection
Posted On December 30, 2021 Making the most of your Microsoft 365 apps requires you to adopt appropriate security measures. Microsoft 365 is one of the best collaboration and productivity tools around. It provides users with seamless communication, scalability and supports remote work with various features. The security is also solid due to a wide array […]
Finding the Right IT Provider: Avoid These 8 Mistakes
Posted On December 30, 2021 Your business can benefit a lot from working with an IT provider. However, you need to avoid several key mistakes when choosing your team. Time spent on trying to figure out the technology you use in your business can be costly. While doing that, you can’t focus on your business needs, […]
Finding the Right IT Provider: Avoid These 8 Mistakes
Posted On December 30, 2021 Your business can benefit a lot from working with an IT provider. However, you need to avoid several key mistakes when choosing your team. Time spent on trying to figure out the technology you use in your business can be costly. While doing that, you can’t focus on your business needs, […]
13 Strategies To Make Your Cybersecurity Failproof
Posted On December 15, 2021 Skilled hackers can easily access your system and steal precious business information. Upgrading your cybersecurity can help address this problem. Taking your cybersecurity seriously is a must. Otherwise, you leave the door open for criminals to compromise your business’s privacy and cause legal troubles. Now, you might think that cybercriminals only […]
How To Choose Your VPN To Boost Protection Against Cyberattacks
Posted On December 15, 2021 Public networks expose your business to security threats. Switching to a VPN can greatly help in reducing those threats. Many companies rely on public networks for communication and data sharing. It allows them to cut costs and allocate their funds elsewhere. However, it also raises several security issues. For starters, the […]
The Importance of Online Reputation Management (And 8 Tips To Improve It)
Posted On December 14, 2021 Online reputation can make or break your chances of landing and retaining clients. That’s why managing this aspect in your business is critical. Your store, whether brick-and-mortar or online, looks great. And your product or service may have struck a chord with the target audience. So, you might think there’s not […]
How Microsoft 365 Defender Can Shield Your Company From Phishing Scams
Posted On December 14, 2021 Phishing can lose you a lot of money and expose sensitive information. Microsoft 365 Defender can dramatically mitigate this risk with several features. Phishing attacks are a severe threat to your business. These fraudulent actions can cause your team members to accidentally share financial, customer, and account information with cybercriminals. How […]
How Microsoft 365 Defender Can Shield Your Company From Phishing Scams
Posted On December 14, 2021 Phishing can lose you a lot of money and expose sensitive information. Microsoft 365 Defender can dramatically mitigate this risk with several features. Phishing attacks are a severe threat to your business. These fraudulent actions can cause your team members to accidentally share financial, customer, and account information with cybercriminals. How […]
Making Your Mobile Devices Safe From Cyberattacks: The 9 Best Practices
Posted On December 14, 2021 The reality is, mobile devices are less safe than desktop computers. Boosting security on such devices is essential if you use them in business. Technological breakthroughs have streamlined your operations in several ways. Primarily, you can now use mobile devices to make your communication and data sharing more convenient. But this […]
The 8 Key Mistakes That Can Cripple Your Business Continuity Plan
Posted On December 14, 2021 The only way to continue your operations in case of setbacks is to enforce a well-thought-out business continuity plan. However, you’ll need to avoid several mistakes when developing your strategy. Your operations may seem efficient and failproof, but the reality is that obstacles can happen at any time. Whether you’ve lost […]
Organizing Your Office Desktop to Improve Productivity – The 7 Tips
Posted On November 17, 2021 Increasing productivity in your business doesn’t just entail optimizing your equipment and sharpening your attention. Decluttering your computer desktop is also essential. A clutter-free office is paramount to improving your productivity. Piles of stationery on your desk can cause you to waste a lot of time searching for a critical document. […]
Immersive Experiences Can Scale Your Business – The 5 Ways Virtual Reality Can Save Your Business Time and Money
Posted On November 17, 2021 Scaling your business doesn’t just entail having suitable systems, staff, or partners. It also includes finding new and innovative ways to save time and money. And that’s where Virtual Reality (VR) technology comes in. What is virtual reality, or VR? VR is the technology that immerses you in a simulated digital […]
How Kohler Uses Office 365 to Create a Culture of Agility (And the 8 Underused Tools That Will Make Your Business More Productive)
Posted On November 17, 2021 There are numerous suites of apps that can improve your productivity. One of them is Office 365, which features an array of underappreciated tools. Office 365 has helped millions of organizations streamline their operations. One of the most famous examples involves Kohler, the manufacturer of kitchen and bath fixtures and plumbing. […]
Is Your Data Secure? 8 Best Practices for Vetting Cybersecurity Vendors
Posted On November 17, 2021 An effective way to bolster your business’s data security is to work with a Managed Service Provider (MSP) or I.T. Service Provider (ITSP). They address network vulnerabilities to prevent cybercriminals from exploiting them. Besides monitoring and organizing your servers, a Managed Service Provider (MSP) or I.T. Service Provider (ITSP) plays a […]
The University That Was Hit by a Cybersecurity Attack (and the 6 Cybersecurity Vulnerabilities You Need to Ensure Your Business Doesn’t Have)
Posted On November 17, 2021 Cybercriminals can take advantage of various vulnerabilities in your company. Patching them up is crucial to protecting your reputation. Taking your cybersecurity seriously is essential regardless of your organization. Otherwise, criminals can easily halt your operations. Take the University of Sunderland as an example. At first, it seemed like they had […]
Creating an IT Compliance Policy – The 7 Things You Need to Consider
Posted On November 17, 2021 Conducting business operations in the digital world is prone to security risks. Mitigating them would be impossible if you don’t have an IT compliance policy. Setting up a robust IT compliance policy in your business is more important now than ever. And it’s because most organizations now depend on digitized services. […]
How Xero Improved Productivity with a Digital Communication Tool (And Five More Technologies You Can Use to Boost Office Productivity)
Posted On October 11, 2021 Higher office productivity leads to faster project completion and happier customers. With these technological solutions, you empower your people to work more efficiently. When a company scales to the point where it has millions of customers spread over 180 countries, effective internal communication is a priority. It’s an even bigger concern […]
Working From Home – The Six Simple Ways to Stay Healthy When You’re No Longer Commuting
Posted On October 11, 2021 With the continuing shift towards remote working, health is an ongoing concern. Find out how to stay healthy even when you’re working from home. The global pandemic resulted in many workplaces implementing work-from-home policies. In doing so, many of these workplaces have discovered that there are benefits to providing employees with […]
5 Biggest Questions About Windows 11 Answered
Posted On October 11, 2021 Microsoft’s latest operating system is starting to take the world by storm. But before jumping ship and upgrading to the new OS, better read this first. It’s finally here. After six years, Microsoft has just released the latest version of its operating system — Windows 11. At a time when computers […]
Seven Ways to Maximize Cloud Solutions for Your Small Business
Posted On October 11, 2021 Cloud computing has been front and centre of the global shift to remote working. Find out how you can maximize this technology for your small business. The onset of the COVID-19 pandemic rendered many business practices obsolete. Face-to-face brainstorming sessions… Team building activities… Even the entire concept of the office… But the […]
The Five Steps for Creating a Business Continuity Plan
Posted On October 11, 2021 How will your business respond when faced with an unexpected situation? With a business continuity plan, you’ll know exactly what steps to take. Leading a small business is a challenging endeavor. According to a January 2021 article published by Entrepreneur, 20% of small businesses fail within their first year of operation. And […]
Explaining Cybersecurity Audits (And the Three Tips for Running One)
Posted On September 29, 2021 You need more than the latest antivirus software to ensure your company’s network is secure. A cybersecurity audit helps you create a complete picture of your security strategy. Cybercrime has grown into one of the epidemics of modern times. In 2018 alone, we saw 812.67 million instances of malware infection. Meanwhile, […]